As a leading IaaS management platform, Spotinst adheres to the highest standard in compliance regulations and follows industry best practices when it comes to securing customer information. Likewise, Spotinst provides its customers with the same level of security and resilience for their own cloud infrastructure.
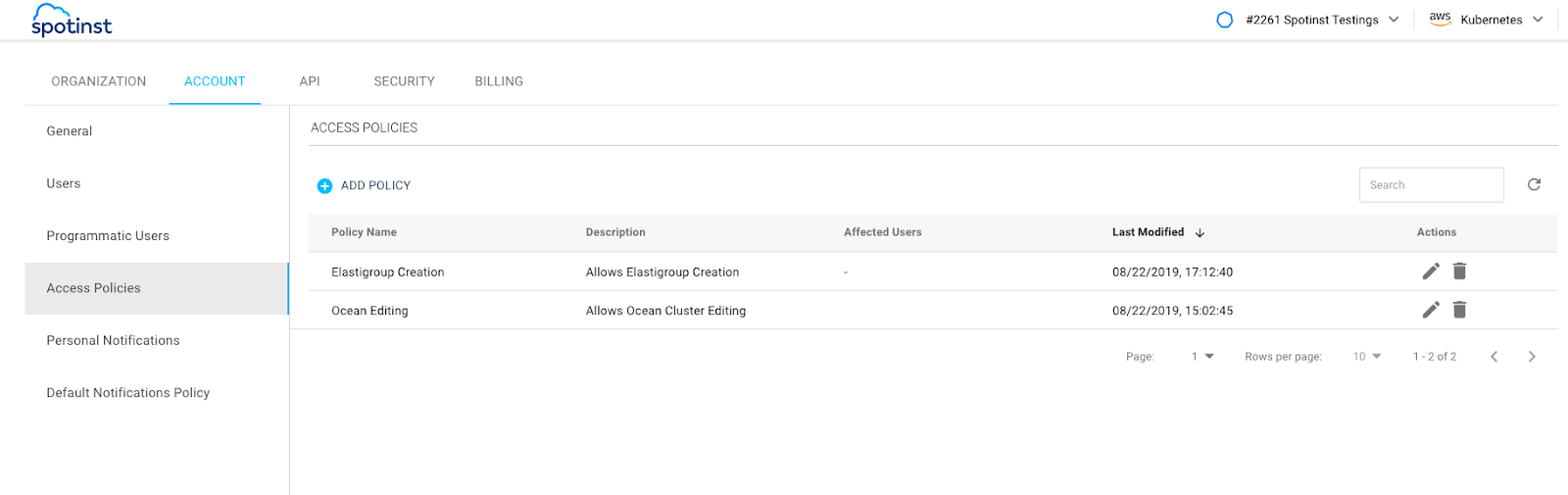
Within that framework, we are happy to announce even greater flexibility and granularity with Access Policies, a policy-based, granular permission system, that is now available for all Spotinst customers.
Up until today, organization administrators could only configure Spotinst account users with one of two roles: Viewer or Editor. Viewers have view-only permissions, while Editors have extensive permissions to create, edit and delete resources. These roles applied to the entire account, so there was no option to modify or restrict them to particular resources.
With the release of Access Policies, admins can now create policies that ‘allow’ or ‘deny’ permissions, with granularity both in terms of the action types, as well as the resources these actions apply to. This enables the configuration of custom policies that can be attached to different user roles within an Organization.
For example, members of the monitoring team could be assigned a policy which allows them to modify existing resources, but restricts creation and deletion. Alternatively, a highly critical production workload can be protected from modification by all users, except for those with the required access permissions.
Organizations can now tailor permissions to meet their access control requirements, ensuring compliance with information security standards and minimizing the risk of human error.
For more information about Access Policies, please refer to our documentation.